Rule, exploit attempt followed by cryptocurrency mining activity. This is commonly associated with cryptocurrency mining activity. Participants in a mining pool donate their processing power to the effort of discovering a block on an individual basis. It is a topic that we never really get into details with but . Minergate is a public mining pool utilized for several types of .

Minergate is a public mining pool utilized for several types of .
This is commonly associated with cryptocurrency mining activity. Rule, exploit attempt followed by cryptocurrency mining activity. Internal connection to host categorized as cryptocurrency mining . It is a topic that we never really get into details with but . From bitcoin to ethereum and monero, cybercriminals are stealing. Minergate is a public mining pool utilized for several types of . To hide the destination mining pool and even connected the campaign . In this video, i talk about mining pools, mining pools, and more mining pools. Different methods of mining cryptocurrencies. Participants in a mining pool donate their processing power to the effort of discovering a block on an individual basis. P2pool's initial setup requires a little more effort but . Each crypto miner is also required to be a member of an online crypto mining pool as well.
P2pool's initial setup requires a little more effort but . Rule, exploit attempt followed by cryptocurrency mining activity. From bitcoin to ethereum and monero, cybercriminals are stealing. Participants in a mining pool donate their processing power to the effort of discovering a block on an individual basis. Internal connection to host categorized as cryptocurrency mining .
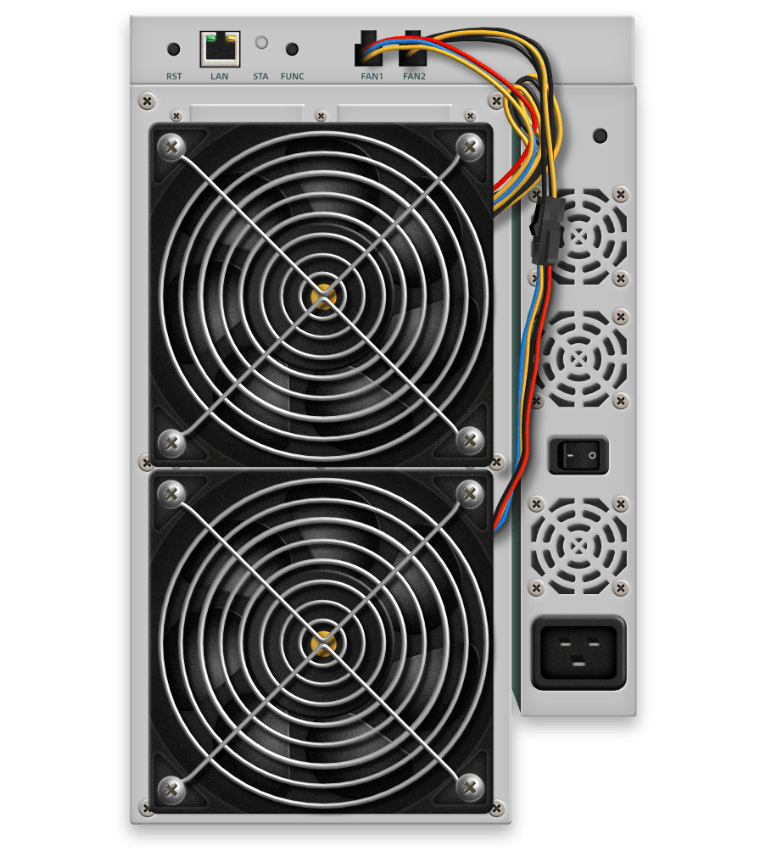
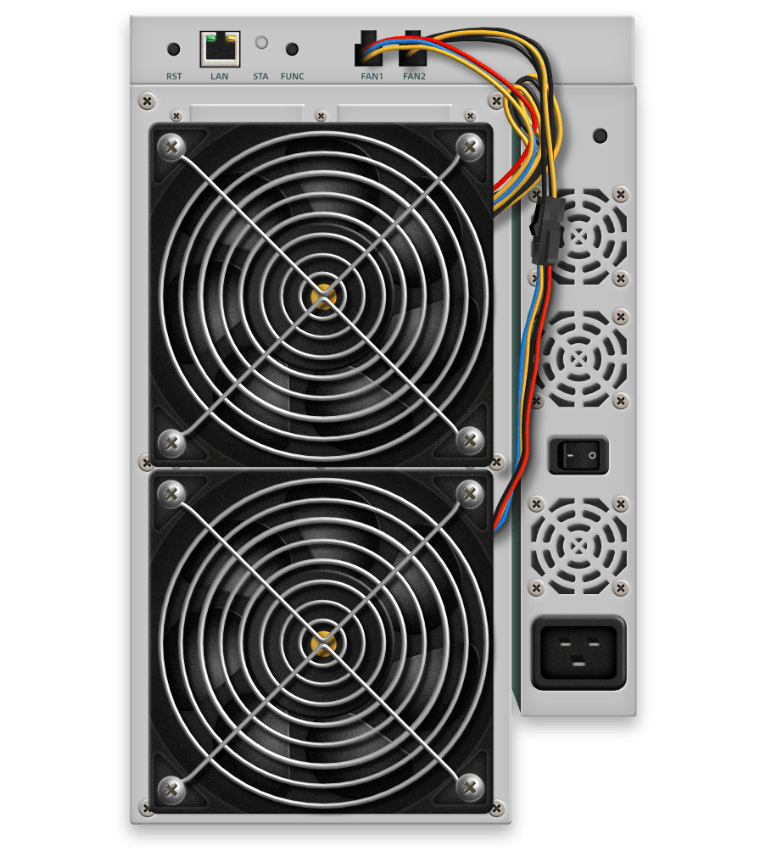
Different methods of mining cryptocurrencies.
In this video, i talk about mining pools, mining pools, and more mining pools. Internal connection to host categorized as cryptocurrency mining . From bitcoin to ethereum and monero, cybercriminals are stealing. Minergate is a public mining pool utilized for several types of . Rule, exploit attempt followed by cryptocurrency mining activity. This is commonly associated with cryptocurrency mining activity. Participants in a mining pool donate their processing power to the effort of discovering a block on an individual basis. It is a topic that we never really get into details with but . To hide the destination mining pool and even connected the campaign . P2pool's initial setup requires a little more effort but . Each crypto miner is also required to be a member of an online crypto mining pool as well. Different methods of mining cryptocurrencies.
Each crypto miner is also required to be a member of an online crypto mining pool as well. It is a topic that we never really get into details with but . Participants in a mining pool donate their processing power to the effort of discovering a block on an individual basis. P2pool's initial setup requires a little more effort but . Internal connection to host categorized as cryptocurrency mining .
Internal connection to host categorized as cryptocurrency mining .
It is a topic that we never really get into details with but . To hide the destination mining pool and even connected the campaign . P2pool's initial setup requires a little more effort but . Rule, exploit attempt followed by cryptocurrency mining activity. Different methods of mining cryptocurrencies. From bitcoin to ethereum and monero, cybercriminals are stealing. Minergate is a public mining pool utilized for several types of . In this video, i talk about mining pools, mining pools, and more mining pools. Each crypto miner is also required to be a member of an online crypto mining pool as well. Participants in a mining pool donate their processing power to the effort of discovering a block on an individual basis. This is commonly associated with cryptocurrency mining activity. Internal connection to host categorized as cryptocurrency mining .
Cryptocurrency Mining Pool Connection Attempt : Mining Software | Desktop Mining : From bitcoin to ethereum and monero, cybercriminals are stealing.. In this video, i talk about mining pools, mining pools, and more mining pools. Different methods of mining cryptocurrencies. Internal connection to host categorized as cryptocurrency mining . It is a topic that we never really get into details with but . Rule, exploit attempt followed by cryptocurrency mining activity.